Kubernetes Dashboard图形化
[TOC]
Dashboard 介绍
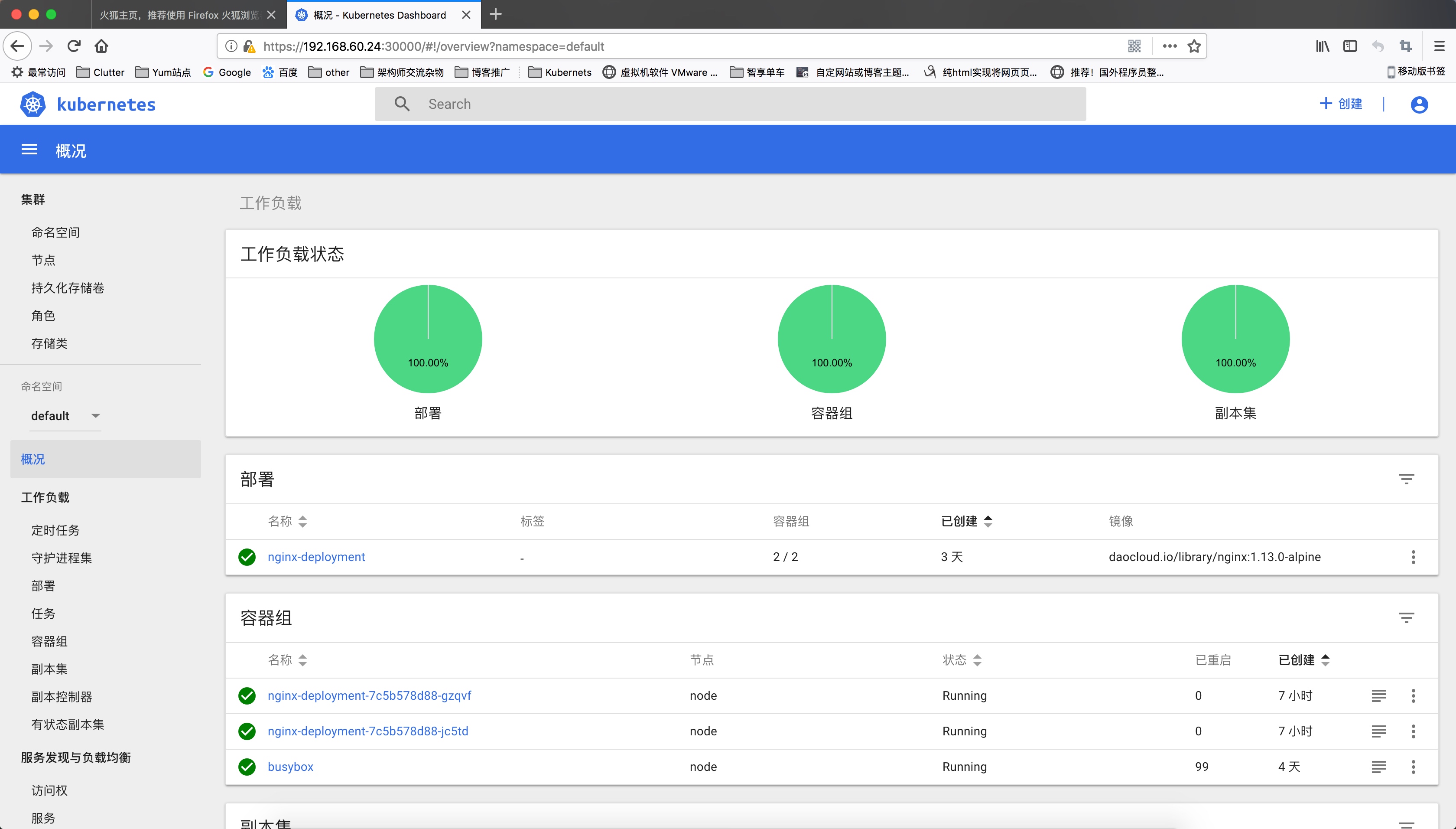
仪表板是基于Web的Kubernetes用户界面。您可以使用仪表板将容器化应用程序部署到Kubernetes集群,对容器化应用程序进行故障排除,并管理集群本身及其伴随资源。您可以使用仪表板来概述群集上运行的应用程序,以及创建或修改单个Kubernetes资源(例如部署,作业,守护进程等)。例如,您可以使用部署向导扩展部署,启动滚动更新,重新启动Pod或部署新应用程序。
仪表板还提供有关群集中Kubernetes资源状态以及可能发生的任何错误的信息。
Dashboard 安装
Dashboard yaml
wget http://down.i4t.com/dashboard.yaml
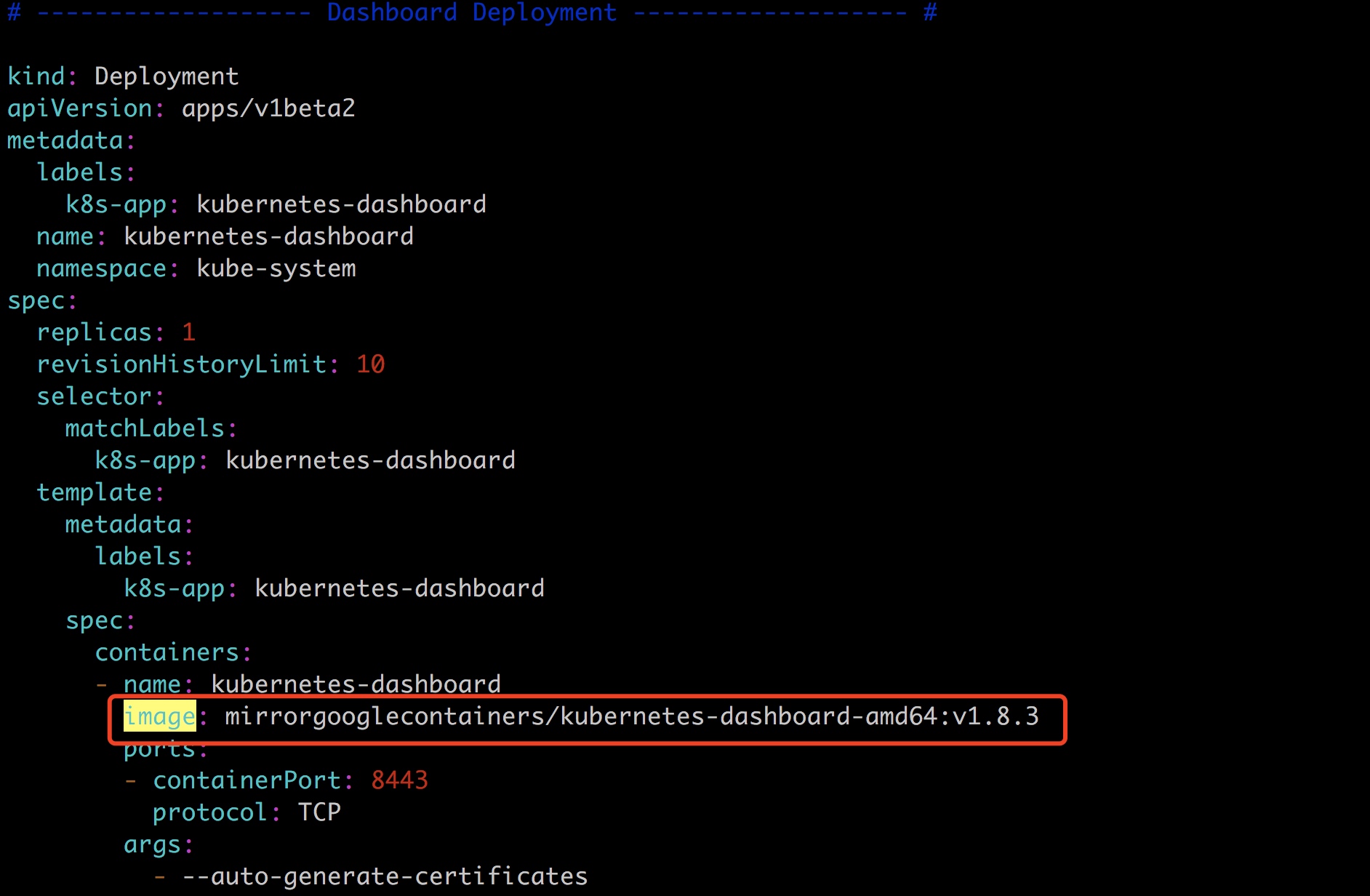
因为默认镜像是在谷歌,因为墙的原因,我们使用国内的镜像
docker pull mirrorgooglecontainers/kubernetes-dashboard-amd64:v1.8.3
优化dashboard.yaml文件(以下步骤可以不进行操作)
使用IP+端口方式启动
官方文档是需要使用proxy方式启动,感觉使用比较麻烦。所以我们指定使用端口的方式
K8s 1.11不兼容Dashboard 1.8.2
修改前
# ------------------- Dashboard Service ------------------- #
kind: Service
apiVersion: v1
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
spec:
ports:
- port: 443
targetPort: 8443
selector:
k8s-app: kubernetes-dashboard
修改后
# ------------------- Dashboard Service ------------------- #
kind: Service
apiVersion: v1
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
spec:
type: NodePort
ports:
- port: 443
targetPort: 8443
nodePort: 30000
selector:
k8s-app: kubernetes-dashboard
添加type:NodePort
暴露端口修改为30000
端口30000-37000直接
生成RBAC文件
#admin dashboard-admin.yaml
cat > dashboard-admin.yaml <<EOF
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: ClusterRoleBinding
metadata:
name: kubernetes-dashboard
labels:
k8s-app: kubernetes-dashboard
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: cluster-admin
subjects:
- kind: ServiceAccount
name: kubernetes-dashboard
namespace: kube-system
EOF
2个yaml文件详情如下:
kubernetes_dashboard.yaml
cat > kubernetes-dashboard.yaml << EOF
# Copyright 2017 The Kubernetes Authors.
#
# Licensed under the Apache License, Version 2.0 (the "License");
# you may not use this file except in compliance with the License.
# You may obtain a copy of the License at
#
# http://www.apache.org/licenses/LICENSE-2.0
#
# Unless required by applicable law or agreed to in writing, software
# distributed under the License is distributed on an "AS IS" BASIS,
# WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
# See the License for the specific language governing permissions and
# limitations under the License.
# Configuration to deploy release version of the Dashboard UI compatible with
# Kubernetes 1.8.
#
# Example usage: kubectl create -f <this_file>
# ------------------- Dashboard Secret ------------------- #
apiVersion: v1
kind: Secret
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard-certs
namespace: kube-system
type: Opaque
---
# ------------------- Dashboard Service Account ------------------- #
apiVersion: v1
kind: ServiceAccount
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
---
# ------------------- Dashboard Role & Role Binding ------------------- #
kind: Role
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: kubernetes-dashboard-minimal
namespace: kube-system
rules:
# Allow Dashboard to create 'kubernetes-dashboard-key-holder' secret.
- apiGroups: [""]
resources: ["secrets"]
verbs: ["create"]
# Allow Dashboard to create 'kubernetes-dashboard-settings' config map.
- apiGroups: [""]
resources: ["configmaps"]
verbs: ["create"]
# Allow Dashboard to get, update and delete Dashboard exclusive secrets.
- apiGroups: [""]
resources: ["secrets"]
resourceNames: ["kubernetes-dashboard-key-holder", "kubernetes-dashboard-certs"]
verbs: ["get", "update", "delete"]
# Allow Dashboard to get and update 'kubernetes-dashboard-settings' config map.
- apiGroups: [""]
resources: ["configmaps"]
resourceNames: ["kubernetes-dashboard-settings"]
verbs: ["get", "update"]
# Allow Dashboard to get metrics from heapster.
- apiGroups: [""]
resources: ["services"]
resourceNames: ["heapster"]
verbs: ["proxy"]
- apiGroups: [""]
resources: ["services/proxy"]
resourceNames: ["heapster", "http:heapster:", "https:heapster:"]
verbs: ["get"]
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: kubernetes-dashboard-minimal
namespace: kube-system
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: kubernetes-dashboard-minimal
subjects:
- kind: ServiceAccount
name: kubernetes-dashboard
namespace: kube-system
---
# ------------------- Dashboard Deployment ------------------- #
kind: Deployment
apiVersion: apps/v1beta2
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
spec:
replicas: 1
revisionHistoryLimit: 10
selector:
matchLabels:
k8s-app: kubernetes-dashboard
template:
metadata:
labels:
k8s-app: kubernetes-dashboard
spec:
containers:
- name: kubernetes-dashboard
image: mirrorgooglecontainers/kubernetes-dashboard-amd64:v1.8.3
ports:
- containerPort: 8443
protocol: TCP
args:
- --auto-generate-certificates
# Uncomment the following line to manually specify Kubernetes API server Host
# If not specified, Dashboard will attempt to auto discover the API server and connect
# to it. Uncomment only if the default does not work.
# - --apiserver-host=http://my-address:port
volumeMounts:
- name: kubernetes-dashboard-certs
mountPath: /certs
# Create on-disk volume to store exec logs
- mountPath: /tmp
name: tmp-volume
livenessProbe:
httpGet:
scheme: HTTPS
path: /
port: 8443
initialDelaySeconds: 30
timeoutSeconds: 30
volumes:
- name: kubernetes-dashboard-certs
secret:
secretName: kubernetes-dashboard-certs
- name: tmp-volume
emptyDir: {}
serviceAccountName: kubernetes-dashboard
# Comment the following tolerations if Dashboard must not be deployed on master
tolerations:
- key: node-role.kubernetes.io/master
effect: NoSchedule
---
# ------------------- Dashboard Service ------------------- #
kind: Service
apiVersion: v1
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
spec:
type: NodePort
ports:
- port: 443
targetPort: 8443
nodePort: 30000
selector:
k8s-app: kubernetes-dashboard
EOF
kubernetes_rbac_dashboard.yaml
cat > dashboard-admin.yaml << EOF
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: ClusterRoleBinding
metadata:
name: kubernetes-dashboard
labels:
k8s-app: kubernetes-dashboard
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: cluster-admin
subjects:
- kind: ServiceAccount
name: kubernetes-dashboard
namespace: kube-system
EOF
使用Nginx 代理方式
如果不使用直接端口通过proxy可以通过下面的方式
#由于1.8之后的kubernetes版本对dashboard做出了限制,所以需要生成一个proxy代理dashboard的web页面
#在任意一个master上执行以下命令
nohup kubectl proxy --address=0.0.0.0 --port=配置端口 --accept-hosts='^*$' > /tmp/proxy.log 2>&1 &
#然后访问页面,apiserver-address换成生成的那个master的IP
http://${apiserver-address}:配置端口/api/v1/namespaces/kube-system/services/https:kubernetes-dashboard:/proxy/#!/login
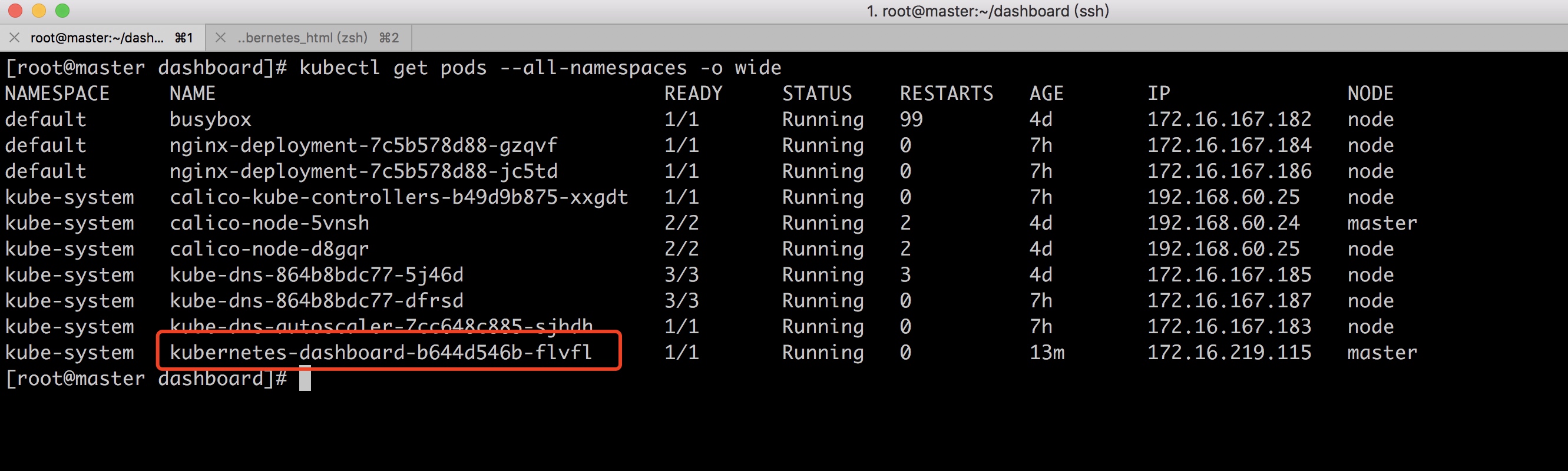
创建dashboard.yaml和rbac
kubectl create -f kubernetes-dashboard.yaml
kubectl create -f dashboard-admin.yaml
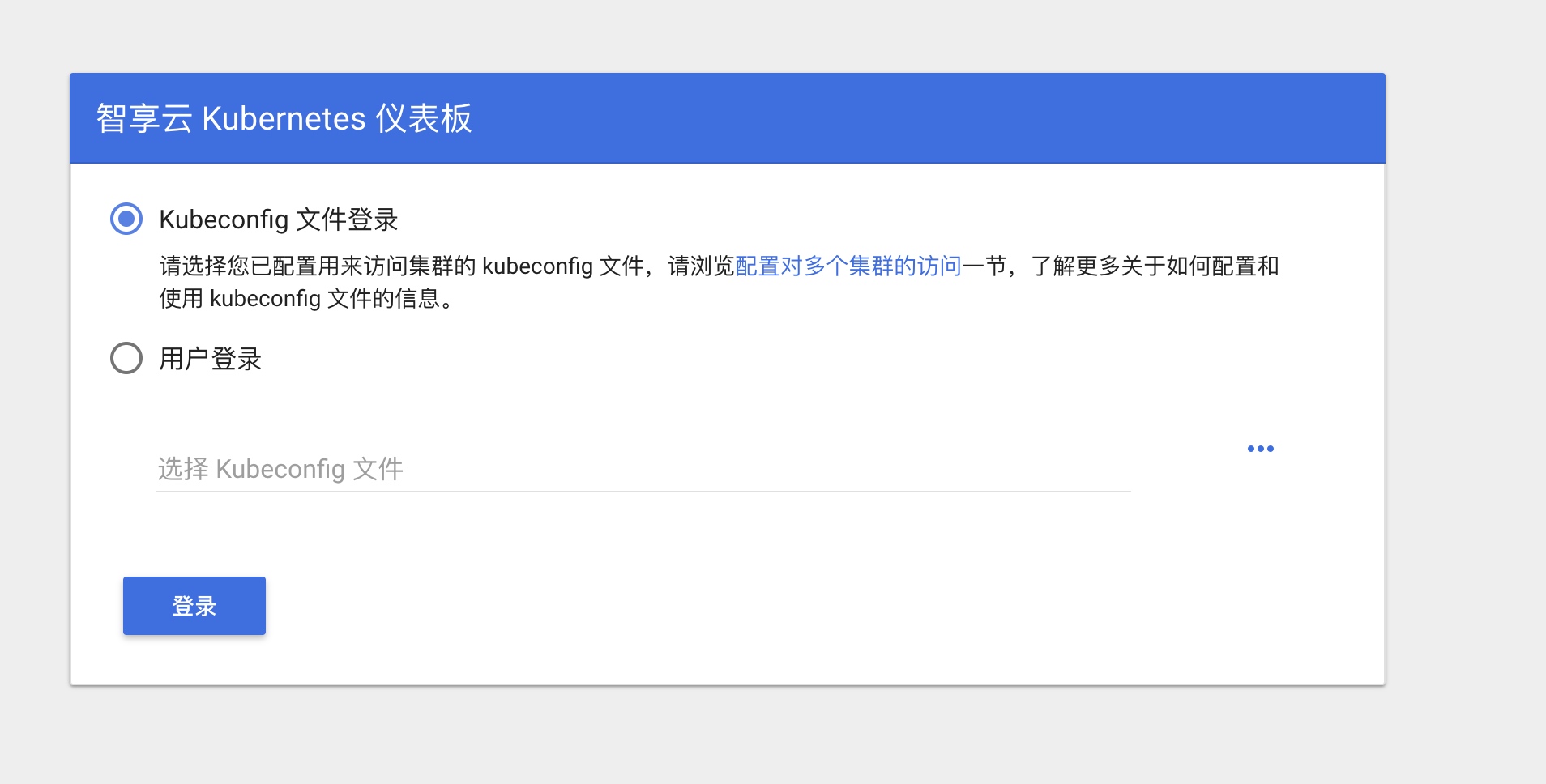
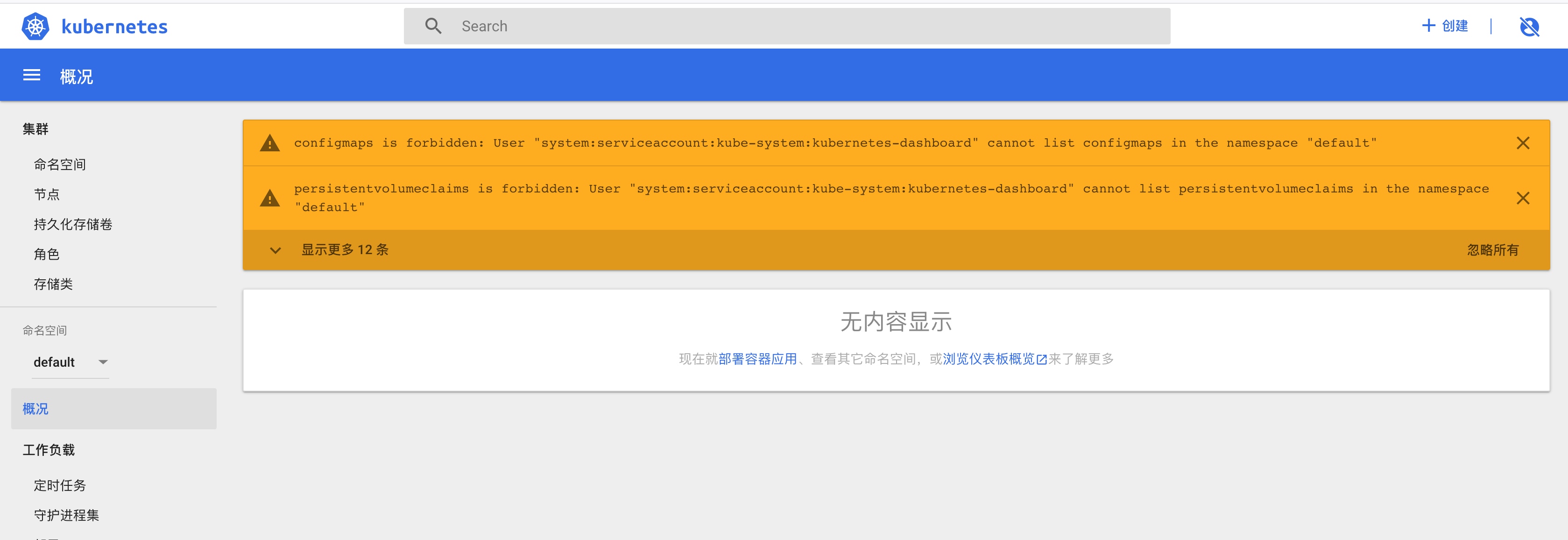
默认情况下部署成功后可以直接访问 https://NODE_IP:配置的端口 访问,但是想要登录进去查看的话需要使用 kubeconfig 或者 access token 的方式;实际上这个就是 RBAC 授权控制,以下提供一个创建 admin access token 的脚本,更细节的权限控制比如只读用户可以参考 使用 RBAC 控制 kubectl 权限,RBAC 权限控制原理是一样的
访问地址:https://192.168.60.24:30000/#!/login
请使用火狐浏览器
本次我们使用ip+端口的方式访问,还可以直接访问nginx代理

我们使用生成的Token访问
kubectl -n kube-system describe secret $(kubectl -n kube-system get secret | grep admin-user | awk '{print $1}') | grep token
设置更规范的rbac
提示:上面的rbac文件用户匿名也可以访问,更安全的规则应该如下
[root@master dashboard]# cat dashboard-admin_new.yaml
kind: ClusterRoleBinding
apiVersion: rbac.authorization.k8s.io/v1beta1
metadata:
name: admin
annotations:
rbac.authorization.kubernetes.io/autoupdate: "true"
roleRef:
kind: ClusterRole
name: cluster-admin
apiGroup: rbac.authorization.k8s.io
subjects:
- kind: ServiceAccount
name: admin
namespace: kube-system
---
apiVersion: v1
kind: ServiceAccount
metadata:
name: admin
namespace: kube-system
labels:
kubernetes.io/cluster-service: "true"
addonmanager.kubernetes.io/mode: Reconcile
[root@master dashboard]# kubectl get secrets -n kube-system |grep admin
admin-token-qm5nm kubernetes.io/service-account-token 3 5m
[root@master dashboard]# kubectl describe secret admin-token-qm5nm -n kube-system
Name: admin-token-qm5nm
Namespace: kube-system
Labels: <none>
Annotations: kubernetes.io/service-account.name=admin
kubernetes.io/service-account.uid=45b7b37e-93eb-11e8-aad1-000c29c0d56b
Type: kubernetes.io/service-account-token
Data
====
token: eyJhbGciOiJSUzI1NiIsImtpZCI6IiJ9.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJrdWJlLXN5c3RlbSIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VjcmV0Lm5hbWUiOiJhZG1pbi10b2tlbi1xbTVubSIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50Lm5hbWUiOiJhZG1pbiIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50LnVpZCI6IjQ1YjdiMzdlLTkzZWItMTFlOC1hYWQxLTAwMGMyOWMwZDU2YiIsInN1YiI6InN5c3RlbTpzZXJ2aWNlYWNjb3VudDprdWJlLXN5c3RlbTphZG1pbiJ9.oyKYKFJTUkwhcR8ZhlyZKzjs9DemMPGOXaSCq3UY7uAq18nQNktQ69QEP38B3uBrLQ5DjlFSjNrs3_O6n_kzSj4PlOjJyj2rGynELljxgrAvK6CNFWWNTDolqrb4o1C2Uw-xRKGdDGYeHvEuif1rZhvVmbIe9KK5sC6zyGPkgSuBDYU3OGMrMIQtr-SdPUzdUXUXMsyU-H9D51AXyRa-aP5LkEJm4iNU9aFAGbsw-STzB3JLkF_UAzH_J127HOvsjF7MPhcFWEHhFt4jYLZGoB_9CwgNaRV7VUBwuxTKLl7B2TC6erl-eOqxFtjRslE0oKp2QiGbapcGchIsJNJYHQaenbFoKbL7NQJzifwtB3owqd_I_BmEl2FEZYSK4Rz9IrAg7srupRE7tWrg4vV_szgTbdsD3tMBVISvLFDbfBI3XbR3zTolpgbTdIZsbqjU-Swke6h3qgAfhzLhkltHCyFvv8bHmM3oCKKlyS6NBpiQEy7MrYKyEtZbsDXA8HKbs_jtKx6GL3mSyviBrsR1DSoThn158mihD9lftCWyLSCYQxMJ58dVY9UaC3EXOXrHg3ntG2nNNFBxHy5W_znptcq972-0YwL_s6PmGVGD1k1H7peh7r9ihk2DJhD1wJFxyo_5JOk0jlBgLmXFFGBpJB7SWL1_158DdsWU6zpxUQU
ca.crt: 2053 bytes
namespace: 11 bytes
[root@master dashboard]# kubectl describe clusterrole cluster-admin -n kube-system
Name: cluster-admin
Labels: kubernetes.io/bootstrapping=rbac-defaults
Annotations: rbac.authorization.kubernetes.io/autoupdate=true
PolicyRule:
Resources Non-Resource URLs Resource Names Verbs
--------- ----------------- -------------- -----
*.* [] [] [*]
[*] [] [*]
[root@master dashboard]#
当我们以这种方式获取到的token才可以登陆 参考文章:https://studygolang.com/articles/11730?fr=sidebar